Oil Politics – Russia – Cyber Politics – China (& N Korea)
○ ○ ○ ○
The end of the calendar year traditionally calls for reflection about the past and hope for the future. This year we pause to consider a number of concerns and ‘keywords’ to keep front of mind…
Economic warfare, geopolitical shots across the bow or not?
Oil decisions not linked to politics
No links to politics Saudis say
Saudi confrontation with Russia
○ ○ ○ ○
President Putin
December 18th – The three-hour news conference with Q&A
Pointedly Putin:
○
“There is no other stability as solid as the support of the Russian people. I don’t think you have any doubts as to whether our key foreign and domestic policy initiatives benefit from such support… We, and I in particular, are acting in the interests of the overwhelming majority of Russians…”
“Only a powerful Russian state can become the main protector of Russian citizens’ interests, regardless of what they are doing, business included…”
○
“You know, at the Valdai [International Discussion] Club I gave an example of our most recognisable symbol. It is a bear protecting his taiga. You see, if we continue the analogy, sometimes I think that maybe it would be best if our bear just sat still. Maybe he should stop chasing pigs and boars around the taiga but start picking berries and eating honey. Maybe then he will be left alone. But no, he won’t be! Because someone will always try to chain him up. As soon as he’s chained they will tear out his teeth and claws. In this analogy, I am referring to the power of nuclear deterrence. As soon as – God forbid – it happens and they no longer need the bear, the taiga will be taken over.
We have heard it even from high-level officials that it is unfair that the whole of Siberia with its immense resources belongs to Russia in its entirety. Why exactly is it unfair? So it is fair to snatch Texas from Mexico but it is unfair that we are working on our own land – no, we have to share.
And then, when all the teeth and claws are torn out, the bear will be of no use at all. Perhaps they’ll stuff it and that’s all.
So, it is not about Crimea but about us protecting our independence, our sovereignty and our right to exist. That is what we should all realise.”
○
JOHN SIMPSON, BBC: Western countries almost universally now believe that there’s a new Cold War and that you, frankly, have decided to create that. We see, almost daily, Russian aircraft taking sometimes quite dangerous manoeuvres towards western airspace. That must be done on your orders; you’re the Commander-in-Chief. It must have been your orders that sent Russian troops into the territory of a sovereign country – Crimea first, and then whatever it is that’s going on in Eastern Ukraine. Now you’ve got a big problem with the currency of Russia, and you’re going to need help and support and understanding from outside countries, particularly from the West. So can I say to you, can I ask you now, would you care to take this opportunity to say to people from the West that you have no desire to carry on with the new Cold War, and that you will do whatever you can to sort out the problems in Ukraine? Thank you!
VLADIMIR PUTIN: Thank you very much for your question. About our exercises, manoeuvres and the development of our armed forces. You said that Russia, to a certain extent, contributed to the tension that we are now seeing in the world. Russia did contribute but only insofar as it is more and more firmly protecting its national interests. We are not attacking in the political sense of the word. We are not attacking anyone. We are only protecting our interests. Our Western partners – and especially our US partners – are displeased with us for doing exactly that, not because we are allowing security-related activity that provokes tension.
Let me explain. You are talking about our aircraft, including strategic aviation operations. Do you know that in the early 1990s, Russia completely stopped strategic aviation flights in remote surveillance areas as the Soviet Union previously did? We completely stopped, while flights of US strategic aircraft carrying nuclear weapons continued. Why? Against whom? Who was threatened?
So we didn’t make flights for many years and only a couple of years ago we resumed them. So are we really the ones doing the provoking?
So, in fact, we only have two bases outside Russia, and both are in areas where terrorist activity is high. One is in Kyrgyzstan, and was deployed there upon request of the Kyrgyz authorities, President Akayev, after it was raided by Afghan militants. The other is in Tajikistan, which also borders on Afghanistan. I would guess you are interested in peace and stability there too. Our presence is justified and clearly understandable.
Now, US bases are scattered around the globe – and you’re telling me Russia is behaving aggressively? Do you have any common sense at all? What are US armed forces doing in Europe, also with tactical nuclear weapons? What are they doing there?
Listen, Russia has increased its military spending for 2015, if I am not mistaken, it is around 50 billion in dollar equivalent. The Pentagon’s budget is ten times that amount, $575 billion, I think, recently approved by the Congress. And you’re telling me we are pursuing an aggressive policy? Is there any common sense in this?
Are we moving our forces to the borders of the United States or other countries? Who is moving NATO bases and other military infrastructure towards us? We aren’t. Is anyone listening to us? Is anyone engaging in some dialogue with us about it? No. No dialogue at all. All we hear is “that’s none of your business. Every country has the right to choose its way to ensure its own security.” All right, but we have the right to do so too. Why can’t we?
Finally, the ABM system – something I mentioned in my Address to the Federal Assembly. Who was it that withdrew unilaterally from the ABM Treaty, one of the cornerstones of the global security system? Was it Russia? No, it wasn’t. The United States did this, unilaterally. They are creating threats for us, they are deploying their strategic missile defence components not just in Alaska, but in Europe as well – in Romania and Poland, very close to us. And you’re telling me we are pursuing an aggressive policy?
If the question is whether we want law-based relations, the answer is yes, but only if our national economic and security interests are absolutely respected.
We negotiated WTO accession for 19 years or so, and consented to compromise on many issues, assuming that we are concluding cast-iron agreements. And then… I will not discuss who’s right and who’s wrong (I already said on many occasions that I believe Russia behaved the right way in the Ukrainian crisis, and the West was wrong, but let us put this aside for now). Still, we joined the WTO. That organisation has rules. And yet, sanctions were imposed on Russia in violation of the WTO rules, the international law and the UN Charter – again unilaterally and illegitimately. Are we in the wrong again?
We want to develop normal relations in the security sphere, in fighting terrorism. We will work together on nuclear non-proliferation. We will work together on other threats, including drugs, organised crime and grave infections, such as Ebola. We will do all this jointly, and we will cooperate in the economic sphere, if our partners want this.”
○ ○ ○ ○
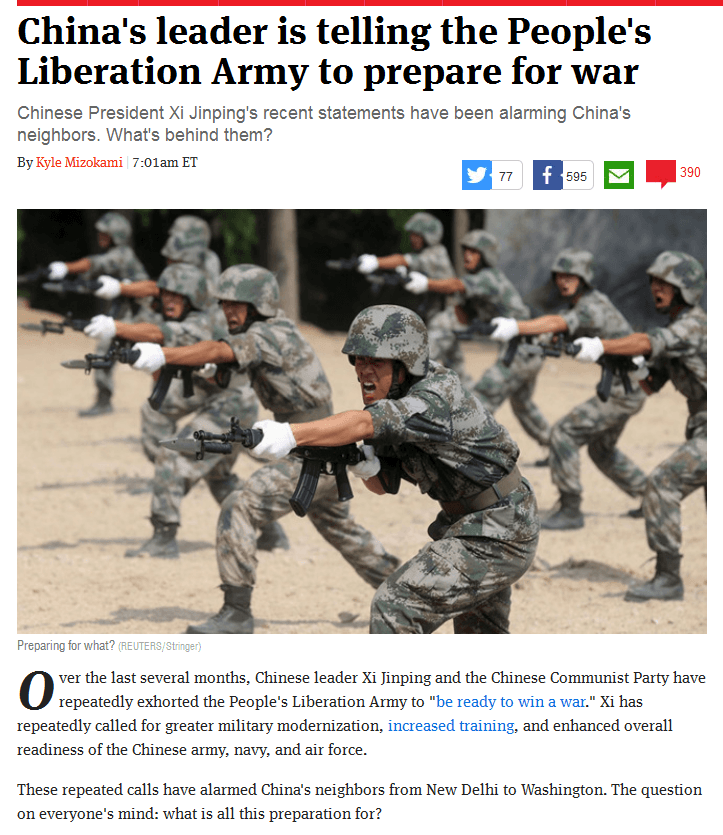
China
-=-=-=-=-=-=-=-=-=-=-
The questions that follow from this ‘prepare for war‘ article are — What? and Why?
What is The Week‘s writer attempting to say here with headlines flaring, and why?
Apart from standing armies (China’s People’s Liberation Army is maintained as the world’s largest) and beyond the worldwide sales of arms, it’s time to contemplate new definitions of war, cyber war, with which war in the future will be waged.
China, and its proxies, and the US and allies, the non-aligned and aligned nations alike, will all engage at varied scales of full-spectrum warfare from afar, digitally, interactively, from cyber intelligence gathering, to analysis, to hit and run, to an array of serious, disruptive, energy/utility aimed, run-of-the-mill ‘denial of service’ onslaughts to critical, irreversible ‘beheading’ of command and control’.
These past weeks have featured a small, initial skirmish. Peter W. Singer, one of the nation’s foremost experts on cybersecurity and cyber war, author of Cybersecurity and Cyberwar: What Everyone Needs to Know and Wired for War, has talked about the hack of Sony’s computer system with a perspective few can wield with authority.
It’s not an act of war
Reactions to the Sony hack: The information that’s come out has pointed the finger at North Korean proxy groups, but it’s been context based.
If we go beyond the less-than-provable connection to North Korea on this less-than-deadly incident, we are brought to the question that has yet to be answered — what constitutes a cyber act of war?
○
Speaking to reporters at the Pentagon on Friday, Pentagon Press Secretary Rear Adm. John Kirby begins to lay down markers, the proverbial red lines are being drawn but in the US few in the media report on this news that underpins the Sony corporation’s hack and possible N. Korea connection.
Consider the ‘grey’ red line that constitutes war by other means, cyber means —
Department of Defense Press Briefing by Rear Adm. Kirby in the Pentagon Briefing Room
QUESTION: Just a follow-on to North Korea. The FBI is blaming North Korea for the attack, and says it has evidence. At what point is it an act of war? And at what point does U.S. Cyber Command react?
KIRBY: First of all, I know of no official determination about the — that’s been made about the source of the attacks on Sony Pictures. So, I’m not in a position to speculate one way or the other. It’s an ongoing investigation and I wouldn’t get ahead of the FBI on that. As I said, we’re part of the interagency discussion about the incident and about options that may be available.
I’m also, you know, not — not able to lay out in any specificity for you what would be or wouldn’t be an act of war in the cyber domain. We take — it’s not like there’s a demarcation line that exists in some sort of fixed space on what is or isn’t. The cyber domain remains challenging — remains very fluid. Part of the reason why it’s such a challenging domain for us is because there aren’t internationally accepted norms and protocols. And that’s something that, you know, we here in the Defense Department have been certainly arguing for.
○
What are contingency planners losing sleep over?
An attack that exploits an entirely new vector giving the victim “zero days” to figure out a patch. The problem is that there is no way to know that they are being implemented until someone, North Korea or someone else, chooses to exploit them.
○
Peering over the horizon, the billions of dollars now going into cyber warfare planning only begin to touch the extent of an Internet of Things (Iot) era in the trillions where connectivity is ubiquitous.
The enterprise will be the largest IoT device market: There will be a total of 23.3 billion IoT devices connected by 2019 across all sectors. The enterprise sector will account for 39% of the roughly 23 billion active IoT devices we expect by the year 2019. The primary barriers to installing the IoT within businesses include the high costs for installation and increasing vulnerability to a cyber attack. (BusinessInsider-Dec 2014)
○ ○ ○ ○
At Strategic Demands, using our knowledge of digital systems, we are beginning to look more closely at the future of the Internet, a “Third Wave”, an Internet that is “Never Offline”, where people and business are ‘Always On’ and the data is being tracked in a cyber future.
Prepare for cyber-connected populations and cyber-connected economies across all sectors. Click “Never Offline” here and there’s GoldmanSachs.
As forecasters attempt to predict the extent of this new world, an Internet of Everything, “Big Data” grows in yet-to-be-defined orders of magnitude. Petabytes flopping into Zetas and quantum quanta are just around the corner.
“Full spectrum adversaries“, defined as an “opponents utilizing full cyber capabilities in combination with military and intelligence” capabilities, are coming. Today’s glimpse of these conflicts can be captured in skirmishes — cyber threats, hacks and attacks.
Cyber-threats
- http://intelreport.mandiant.com/
- http://www.acq.osd.mil/dsb/reports/ResilientMilitarySystems.CyberThreat.pdf
Cyber Hacks & Attacks
Dec 22
Someone disconnects N Korea, Who?
○
○
Dyn Research
Update: All four North Korean prefixes have been restored to service at 01:46 UTC, after a national outage of nine and a half hours. Traffic is routing through China Unicom, just as before.
Dec 23 / Washington Post
At a news conference, Hua Chunying, a spokeswoman for China’s foreign ministry, said the United States and North Korea needed to communicate directly.
She said Beijing had not seen proof of who was behind the attack on Sony. “We need sufficient evidence before drawing any conclusion.”
From the Washington Post correspondent in China —
The ‘question of who pulled the plug (if it was a plug) remained a mystery’. The ‘who’ question remains — and behind the scenes Anonymous watchers watch…
Was the hack the work of North Korea? Security expert Marc Rogers says maybe not / Even though the FBI pins it on North Korea
The Chinese public position is that the reporting on North Korea’s involvement is without proof.
The attack on Sony has put Beijing in a difficult position. On the one hand, it wants to cooperate with the United States on cybersecurity and cyberterrorism, but on the other it does not want to alienate its allies in North Korea…
Bloomberg BusinessWeek quotes an anonymous source on Monday as saying China had agreed to start its own investigation into the incident…
Liu Deliang, a professor and cyber law expert at Beijing Normal University, said he doubted China would agree to such an investigation, arguing that Beijing was keen to first set up an international code of conduct and legal framework to govern the Internet, with an independent third party established to look into cyberattacks.
But other experts said Beijing’s desire to be seen as a responsible power in global Internet governance means it might be willing to look into the attack on Sony.
“The conclusion that North Korea attacked Sony is based on inference. So is the conclusion that the United States attacked North Korea. The incidents have not been proved yet,” said Shen Yi, an associate professor in the School of International Relations and Public Affairs at Fudan University.
“Tracking down attackers is always the most difficult task, because it’s hard to know if the IP address belongs to a ‘springboard’ or is the original source…
○
Dec 3 / BEIJING – Xinhuanet
China and the United States are mapping out rules for the Internet, said China’s web chief Lu Wei in Washington on Dec. 2, according to a report by the China News Service.
○
One more excerpt from Marc Rogers’ statement that he does not firmly believe that North Korea is the principal actor in the Sony hack. In previous time, this could be considered a “provocation”, which has historically become a ’cause for war, a casus belli. In this case, the the accusation against North Korea, and subsequent downing of the North Korean infrastructure has not led to escalation. Is it a force majeure event? The incident has become more of a warning than a cause, but it strikes us as consequential. ‘Rules of cyberwar’ are being formulated as a result of this cyber ‘incident’.
Rogers: I am no fan of the North Korean regime. However I believe that calling out a foreign nation over a cybercrime of this magnitude – something serious enough to go to war over – should not be taken lightly. The evidence used to attribute a nation state in such a case should be solid enough that it would be both admissible and effective in a court of law. As it stands, I do not believe we are anywhere close to meeting that standard.
○
On this thought, that the US and China are formulating rules for the Internet — and potentially rules of when cybercrime and cyber hacks and attacks become cyberwar, we leave you — and wish all a Merry Christmas — good will and good tidings as the New Year arrives …






“The bear never asks permission from anyone… he will never give up his forest to anyone.” “Our American friends are cutting off the branch they are sitting on.”
“We aren’t on the offensive, we aren’t attacking anyone, we are only defending our interests.”